Download PDF
RCA TRAINING
Root Cause Analysis training by Sologic provides the tools, skills, and knowledge necessary to solve complex problems in any sector, within any discipline, and of any scale. Learn MoreSOFTWARE
Sologic’s Causelink has the right root cause analysis software product for you and your organization. Single users may choose to install the software locally or utilize the cloud. Our flagship Enterprise-scale software is delivered On Premise or as SaaS in the cloud. Learn MoreREAD THIS FIRST!
We need to disclose that this EXAMPLE RCA is based solely upon publicly available information from a variety of sources (mostly newspaper articles) and not from any independent investigation conducted by Sologic. Sologic has not investigated this incident in any official capacity, and we do not want to imply that we were in any way associated with this event. The only purpose of this root cause analysis report is for it to be used as an example for our students and other interested parties.
A root cause analysis has two primary goals: 1) Organize a wide array of information from disparate, reliable sources in a way that makes it easier to understand, and 2) Identify a set of evidence-based solutions to present to decision makers.
 Problem Setup:
Problem Setup:
After determining the appropriate Focal Point, setting up the first level of causes is extremely important. We chose the Focal Point “Global Impact from WannaCry Malware” because it breaks down nicely into the following causes:
- Data from more than 250,000 computers in 150 countries encrypted: This cause provides us a bridge into the largest part of the analysis examining both the malware as well as how it the infection spread.
- Impact limited by "Kill Switch" activation: This branch introduces a limiting aspect to this particular event. It would have been much worse if not for this action. We often include causes at the top level that allow us the opportunity to examine the extent of the impact, whether limiting (as in this case) or exacerbating (which also happens). In either case, the cause provides value in that it completes the top-level picture and potentially identifies opportunities for solutions.
Here is how it sounds when put back into narrative form:
“The global impact from the ‘WannaCry’ malware attack was caused by the encryption of data from more than 250,000 computers in 150 companies with an encryption method that was nearly impossible to decode. However, the overall impact was limited by the activation of a ‘kill switch’ embedded in the malware.”
Or something like that.
Follow along with the cause and effect chart as you read the following summary statement.
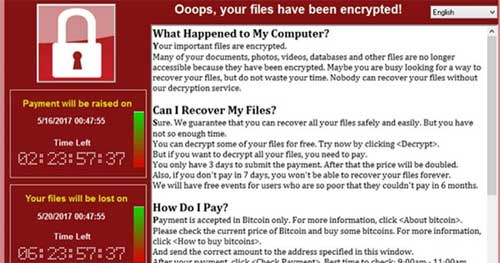
On May 12, 2017 people around the world were greeted by the following splash message:
“Oops, your files have been encrypted!”
The message goes on to explain that, in order to decrypt the files, the user must send a bitcoin payment as ransom. Payment amounts started at about $300, but the message threatens to escalate the amount the longer the person waits. There was no guarantee that paying the ransom would actually unlock the user’s data. But what choice did they have? The encryption method was essentially unbreakable. So unless users had a very recent unencrypted backup, they were basically out of luck.
Many organizations were impacted, including the British National Health Service, Spain's Telefonica, Fed Ex, and Deutsche Bahn, along with thousands of other users. The hack exploited a vulnerability in Microsoft Windows, specifically an app called Server Message Block (SMB). SMB has file-sharing functionality and was intended to facilitate the easy transfer of files between users on the same network. But it also provided an unprotected pathway into the users computer.
A secretive organization called “The Equation Group”, supposedly associated with the National Security Agency (NSA) found this vulnerability at some point in the past – we don’t know when. Rather than give Microsoft a heads-up, the NSA kept it secret and developed offensive cyber weapons that took advantage of the vulnerability. But an outsider gained access to the files containing these weapons, and then provided them to a hacker group calling themselves “The Shadow Brokers.”
The Shadow Brokers’ original stated intent was to auction the Equation Group files to the highest bidder. On August 13, 2016, they posted a message with links to some sample data, along with instructions for how to bid on a password that would provide access to the entire library of files. They apparently had no takers, so on October 31, 2016 they released additional information to help stir up demand. Again, apparently no one was interested. So on November 25, 2016, they tried a third time – this time releasing screen shots of file names. And again, they got nothing. They let several months pass until April 8, 2017 when they released a password to decrypt the files they originally released months before. And finally, out of apparent frustration, on April 14, 2017, they released access to the entire library of files.
Someone (or many someone’s) must have been watching the Shadow Brokers. On March 14, 2017, Microsoft began releasing patches to the fix the SMB vulnerability. But Microsoft wasn’t the only one watching. After the April 14, 2017 message, someone (reportedly hackers linked to North Korea’s spy agency, the Reconnaissance General Bureau) put it all together. And on May 12, 2017, they released it to the world.
How the Malware Works:
The name of the payload (the code that does the damage) is EternalBlue. EternalBlue is not exceedingly complex – it simply searches a hard drive for files, encrypts them, passes the ransom message to the user, and then propagates itself to other computers on the same network. But first, it must gain access to a vulnerable computer. It does this through the Server Message Block file transfer feature. In some cases, SMB simply allowed the payload to pass through and install itself. Remember, SMB is used on shared networks, so inbound files would be automatically trusted. In other cases, Windows would not allow software to simply load itself, but instead required proof that the user wanted the software installed. Most of us are familiar with this process – we must enter our username and password to install software. So, included with the malware was a separate file called “DoublePulsar.” DoublePulsar is what is known as a backdoor application. Its purpose is to provide validation to the operating system that it’s okay to load an application.
It was a 1-2 punch. SMB provided the means to transfer files to vulnerable computers, of which there were many. EternalBlue installed itself, locked up the user’s data, and then propagated itself to other computers on the same network. And, if it couldn’t install itself, DoublePulsar provided the validation required for the install to proceed.
The spread of this malware would have been much more extensive were it not for the actions of an employee of a web security firm. He was watching the attack take shape and was able to infect an isolated computer, thereby allowing him to examine the malware. In studying the malware code, he noticed that it utilized a web URL. It is standard protocol to attempt to purchase URLs embedded in malware. At the time, he did not realize the impact of this purchase. However, once he bought the URL, he set used it to set a “trap” to capture incoming requests. This essentially killed the spread of the malware in that it could not install or propagate to other networks.